Protect, Detect, Respond & Recover: How Our Ransomware Tools Just Got Even Better
Nasuni offers advanced ransomware protection designed to help organizations prevent, detect, respond to, and rapidly recover from attacks. After listening to our customers and gathering their feedback about our recently released Ransomware Protection add-on service, we’ve bolstered our offering. I’m thrilled to share that the soon-to-be-released Nasuni File Data Platform version 9.9 will give our customers the opportunity to take advantage of several powerful new Ransomware Protection add-on features.
October 19, 2022
The ransomware threat isn’t fading away. Ransomware hit 66% of mid-sized organizations last year. Average payments jumped from $170,000 in 2020 to $812,000 in 2021. These are harrowing statistics, but not to our customers.
Nasuni offers advanced ransomware protection designed to help organizations prevent, detect, respond to, and rapidly recover from attacks. Yet we’re always trying to get better. After listening to our customers and gathering their feedback about our recently released Ransomware Protection add-on service, we’ve bolstered our offering. I’m thrilled to share that the soon-to-be-released Nasuni File Data Platform version 9.9 will give our customers the opportunity to take advantage of several powerful new Ransomware Protection add-on features.
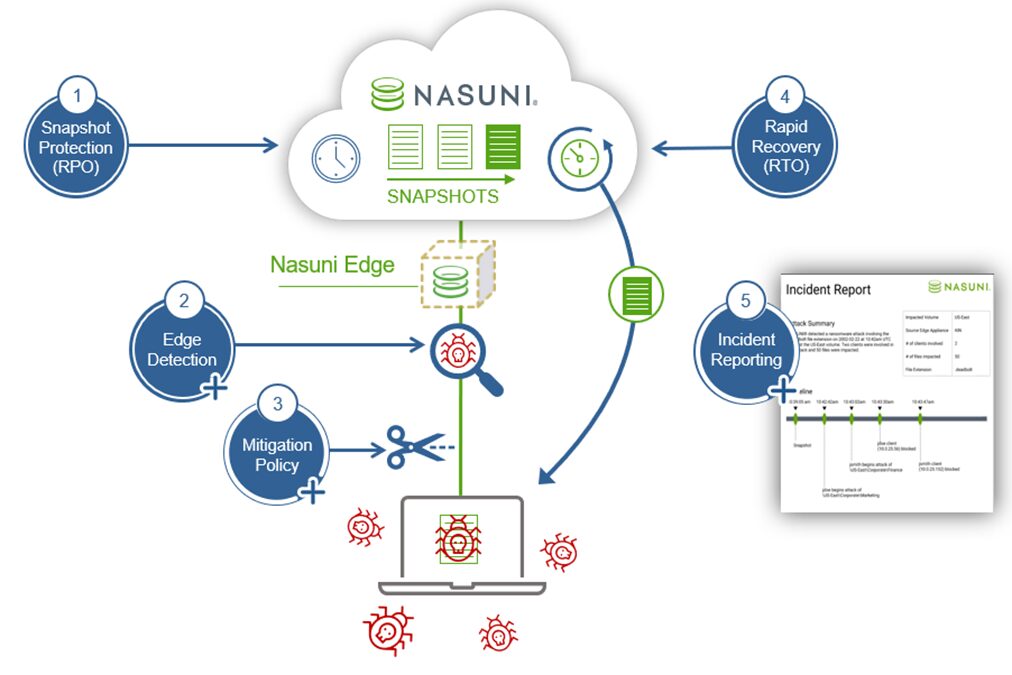
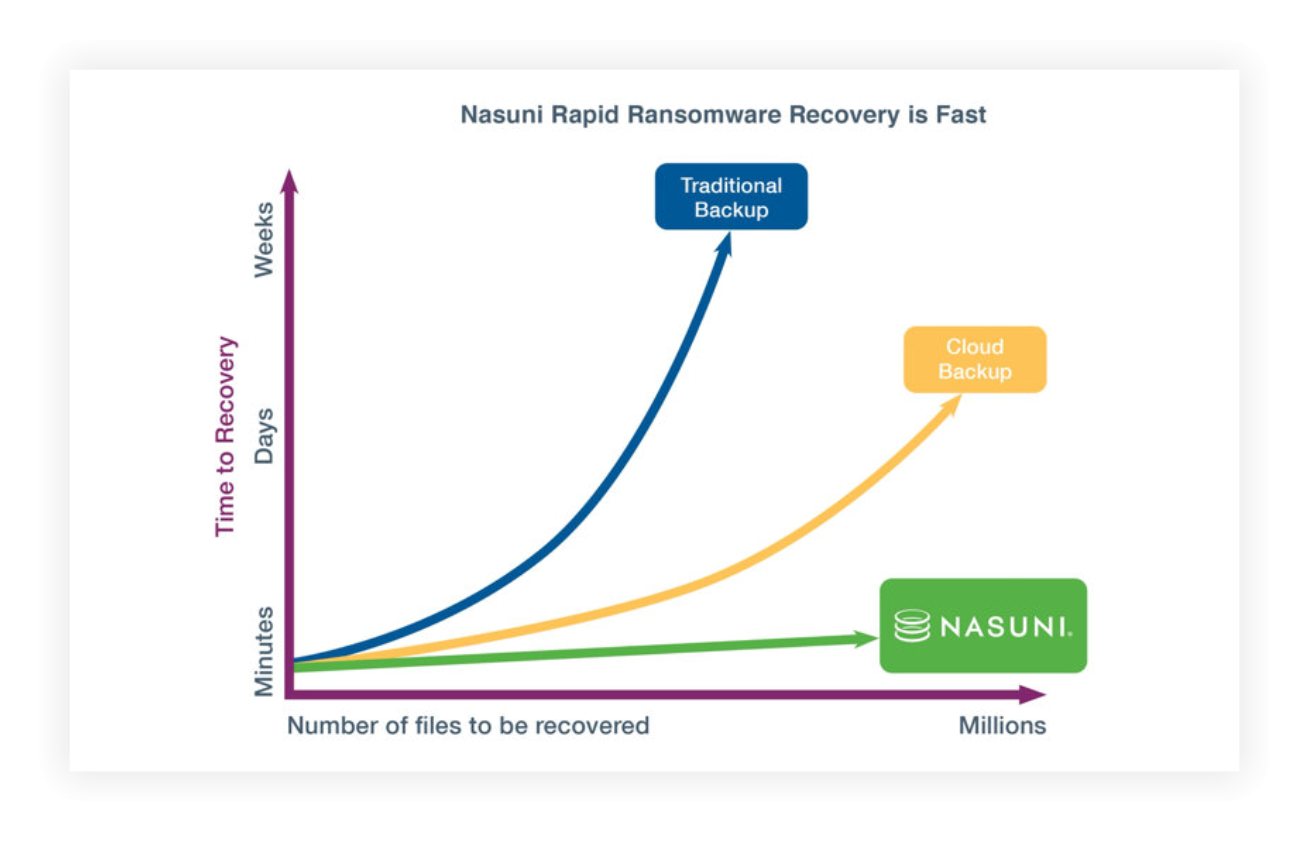
Before I highlight these new tools, I should note that the Nasuni File Data Platform’s core capabilities are already leading the way in helping organizations protect and recover their file data. Files are versioned to the cloud as frequently as every minute and stored as immutable objects, giving you granular Recovery Point Objectives (RPOs). In the event of a ransomware attack, you can quickly point back to clean, healthy versions of files before they were encrypted. Since the gold copies of all files live in the cloud, you don’t have to move massive file volumes or rebuild file servers. Instead, Nasuni allows you to recover millions of files in minutes — all without paying a ransom.
To our current customers or readers of this blog, this is probably old news. We have already shared many customer ransomware recovery stories. This new update strengthens our overall ransomware protection solution by enhancing our customers’ ability to detect and respond to these attacks. This is an add-on Ransomware Protection service to the Nasuni File Data Platform, but customers who choose to deploy it with the latest release will benefit from a complete system that allows you to protect, detect, respond, and recover.
“Nasuni continues to improve and add value their product. With the latest Nasuni release we have enhanced our business resiliency strategy by enabling the ability to detect, alert and respond to ransomware attacks, as well as rapidly recover from any possible data encryption,”
– Brian Erickson, IT Acquisition Implementation Leader, APi Group.
Protect
Our Continuous File Versioning technology, which is included in the platform, creates the first line of defense through automatic, infinite snapshots that generate strong RPOs. This feature is included with the Nasuni File Data Platform and works automatically in the background with no management or oversight required.
Detect
Live detection of suspicious events at the edge has been part of the Ransomware Protection add-on service since the outset. The sooner you can detect suspicious activity, the sooner you can quarantine the attack and limit the extent of the damage. This translates into faster recoveries and minimizes business disruption.
What we’re adding in Nasuni 9.9 are some exciting new mitigation features. Every organization is different, so we designed this feature to be customizable. You can set your own thresholds and tolerance levels and choose the number of violations within a selected time span. So, for example, you can tune the settings so that you only receive alerts if the service logs, say, 100 violations in 5 minutes.
Respond
Once you’re aware of the attack, you have to act. With the new features of the add-on service, you can set up the system so that when a certain threshold is passed, the source of the suspicious activity is automatically cut off, which prevents the attack from spreading.
We also added incident reporting to the add-on service for version 9.9. So, you can generate easy-to-read reports with key details, including the number of clients involved, files impacted, and the timeline of events, including the timing of the last clean snapshot. This feature is especially valuable during the recovery phase, since it shows you exactly what time you need to point back to and enables the surgical recoveries that set Nasuni apart.
Recover
Once the attack has been identified and quarantined, IT can use the platform’s built-in rapid ransomware recovery capabilities to point back to healthy versions of the impacted files and restore normal operations. As with Continuous File Versioning, this is included with the platform, and a direct benefit of Nasuni’s unique cloud-native technical architecture.
The reporting and auditing capabilities outlined above will help our customers share the specifics of the attack and their response within their organization, and hopefully identify ways to minimize the chances that it happens again.
Internally, we are very excited about the features attached to this new release, as we feel they truly differentiate our platform in the ransomware space. Nasuni already protects your file data and enables rapid recoveries, but now you’ll be in a better position to effectively take advantage of these great innate features. The new release and add-on service benefits will make it easier to quickly identify the source of the attack at the edge; isolate and cut it off before it spreads too far; and generate a comprehensive incident report to show what happened and exactly what you need to do to initiate a rapid restore. Ultimately, we’re making it easier for you to get back to business as usual even faster.
These newest features to our Ransomware Protection add-on service are going to have a powerful impact across our growing customer base, and I’m excited to see what our product and engineering teams come up with next.
